Welcome to 3ERP's blog
We share information, tips and things we've learned from our years in the rapid prototyping and manufacturing industry.
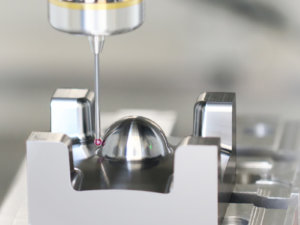
In the realm of medical advancements, CNC machining revolutionize the manufacturing of medical devices with unparalleled precision and reliability. Below you will go into the world of CNC machining for the medical industry, exploring its suitability, methods, materials, applications, advantages, challenges, and guidelines for selecting the best CNC machine suppliers. What Makes CNC Machining Suitable […]
Exploring the universe of machining materials opens doors to an array of possibilities and challenges in the manufacturing sector. In this article we want to emphasize materials suitable for conventional machining, setting them apart from those used in CNC machining. Our journey will cover everything from the historical evolution of these materials to future trends […]
The injection molding process is not without its challenges, particularly when it comes to defects that can compromise quality. Recognizing and addressing injection molding defects is essential for manufacturers to ensure product quality, reduce waste, and optimize production efficiency. This guide goes deep into the most common issues, offering insights into their causes and outlining […]
Acrylic (PMMA) is a highly desirable material due to its strength, toughness, and transparency. But relying on conventional machining processes to cut acrylic can be a complicated procedure: the material is highly fragile and any excess force can cause unwanted breakages. CNC machining, however, offers a reliable way to fabricate acrylic parts safely, with a […]
Rapid injection molding method is revolutionizing how products come to life, blending efficiency and speed with engineering. This process makes it possible to manufacture many durable consumer and industrial items cheaper than everything else. It produces around 32% of plastics by weight. What is Rapid Injection Molding? Rapid injection molding is a type of injection […]
Diving into the world of manufacturing, one cannot overlook the pivotal role of injection molding machines. These devices are the unsung heroes behind the multitude of plastic products we use daily. From simple household items to intricate automotive components, the versatility and efficiency of injection molding machines make them indispensable in the production landscape. What […]
In the vast world of manufacturing, injection molding stands as an essential technique, used for creating a myriad of products with precision and efficiency. Let’s explore the multifaceted types of injection molding processes, each tailored for specific applications, materials, and advantages. The essence of injection molding, a process marrying innovation with technology, propels industries forward, […]
Dive into the art and science of mold making, an essential and intricate process that shapes the backbone of manufacturing industries worldwide. From the precision crafting of automotive parts to the delicate creation of medical devices, mold making enables the mass production of items with unmatched accuracy and consistency. This guide unravels the layers behind […]
For every CNC machining project, achieving the ideal surface finish is more than just an aesthetic choice—it’s an important factor that influences the functionality, durability, and performance of the machined parts. This comprehensive guide delves into the nuances of CNC surface finishes, offering insights into processes, comparisons, and the selection of suitable finishes for various […]
Galling is a common problem with metal parts. It happens when two sliding metal surfaces unexpectedly stick to one another, causing frictional damage and ultimately unwanted cold welding. Most often seen in sliding parts like threads, fasteners, bearings, cylinders, and pistons, galling can also occur during metalworking — when microscopic pieces of the workpiece adhere […]